Why Build Reviews Are Essential
Build reviews, both for internal and cloud-based systems, are vital for benchmarking system builds against recognised cyber-security standards such as CIS (Center for Internet Security), ISO (International Organization for Standardisation), SANS Institute, or NIST (National Institute of Standards and Technology). These reviews are not just about ticking boxes; they are about understanding how secure a system configuration is in a real-world context, is effective in defending against attacks. With the goal to forestall future attacks by identifying and remedying the identified configuration weaknesses.
System hardening, a critical first step, that involves configuring systems securely by removing unnecessary functionalities that might introduce security vulnerabilities. However, the journey towards a secure system doesn't end with system hardening. Regular updates, patches, and thorough build reviews using the latest Cyber-Security standards are essential to maintain and enhance the system's security posture over time.This continuous process helps maintain and progressively enhance the security posture of the system, ensuring that a robust defense in depth multilayered security exists to protect against emerging and zero day threats.

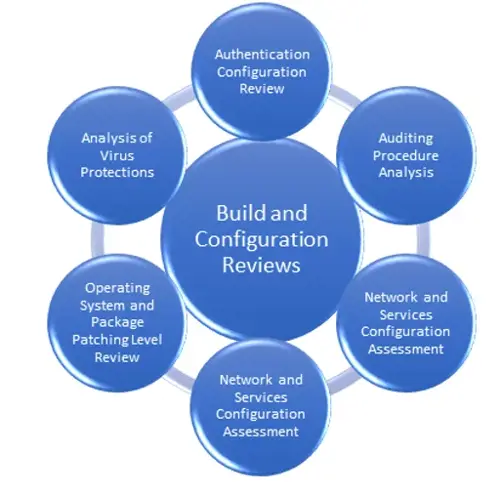
Types of Build and Configuration Reviews
Workstation Build Review
- Reviewing a standard user workstation involves a thorough examination of the system to identify vulnerabilities and exploitable data accessible to low-privileged accounts. This type of review forms a crucial part of organisational security by ensuring that everyday user environments are secure from internal and external threats. Workstation reviews often focus on the security settings, installed applications, system updates, and endpoint protection mechanisms to determine the potential risks that might compromise data integrity and confidentiality.
Server Build Review
- Server Build Reviews are critical for ensuring the security of servers, which often serve as the backbone of organizational IT infrastructure. These reviews assess both physical and virtual servers to safeguard critical business data and functionality against potential attacks. This involves evaluating the server's operating system configurations, services running on the server, and the security of applications hosted. Server reviews help in maintaining the integrity and availability of business-critical services, whether these servers are accessed publicly or kept private.
Mobile and MDM Review
- Mobile devices are integral to modern business operations, but they also introduce significant security risks if not properly managed. Mobile Device Management (MDM) reviews focus on the policies and tools used to manage and secure company mobile devices. This includes the enforcement of strong encryption practices, securing data such as emails, documents, and login credentials, and ensuring that lost or stolen devices can be located, locked, or wiped remotely. MDM reviews help in protecting sensitive information on mobile platforms against unauthorized access and loss.
Firewall Configuration Review
- Firewalls act as the gatekeepers for an organization’s networks, controlling the flow of incoming and outgoing network traffic based on a set of security rules. A Firewall Configuration Review ensures that these devices are configured to provide optimal protection. This type of review assesses the rules and policies set on the firewall to determine their effectiveness in protecting against intrusions and data exfiltration. Ensuring that firewalls are correctly configured is crucial for preventing unauthorized access and securing both public and private networks.
Each of these reviews is designed to address specific aspects of network and system security, ensuring comprehensive coverage across all critical areas of your IT environment. By conducting detailed build and configuration reviews, organisations can significantly enhance their security posture and reduce the risk of potential cyber threats.
Overview Of The Build Review Process
Servers often contain sensitive information, making them prime targets for attackers. The assessment process we adopt for server build reviews can also be applied to auditing other devices. For more detailed information on network device configuration reviews, please see our 'Firewall Rule and Configuration' section.
Our Approach
Our methodology for conducting build reviews is both thorough and adaptable, designed to meet the unique needs of each organization.
To begin assessing your server's security, we require:
- An account with local administrator privileges.
- A management login channel, specifically tailored to the systems under review.
Utilising a combination of host-based audit tools, custom scripts, and manual checks, we dive deep into the top three layers of the defence in depth model: Host, Application Layer, and Data. This multi-layered approach ensures that we leave no stone unturned, from the operating system and core services to the applications and data that are crucial to your business operations..

Defense in Depth - Multilayered Security
- Defence in Depth: Host
The first layer of our review focuses on the operating system and core services. Here, we aim to uncover any potential vectors that could be exploited by attackers to gain unauthorised access or control over your systems. - Defence in Depth: Application
Moving up to the application layer, we scrutinize the software and services that are integral to the server's role. This includes everything from web servers and database software to critical applications like Active Directory, assessing them for vulnerabilities that could compromise your security. - Defense in Depth: Data
At the pinnacle of our review process, we ensure that the data stored on your systems is adequately protected, aligning with the level of protection the system claims to offer. This stage is crucial for safeguarding sensitive information from unauthorized access or breaches.
Tailored Build Reviews
While we draw on a variety of hardening guidelines and standards, including those from NIST, CIS, software publishers like Microsoft, and CESG, we understand that each organisation has unique security needs. Therefore, we also offer customized build reviews, tailored specifically to your business requirements and security objectives.
Detailed Reporting
Upon completing our review, you will receive a comprehensive technical report that details all identified issues, recommended solutions, and an executive summary for easy understanding. We prioritize the immediate notification of any severe vulnerabilities discovered during our review, ensuring a collaborative and proactive approach to securing your systems.
In conclusion, build reviews are an indispensable component of a robust cyber-security strategy, providing the insights and actions needed to protect your systems and data effectively. By partnering with us for your build review needs, you can rest assured that your cyber-security posture is not just compliant, but truly secure.

For More Information Please Contact Us

ACCREDITATIONS






