Physical Security Audit
Introduction
In the intricate tapestry of cyber-security, while digital defense is vital, it is the fortress of physical security that anchors the entire security apparatus. A Physical Security Audit doesn't merely review door locks; it gauges an organization's resilience against a spectrum of tangible threats, evaluating an organization's existing measures to protect its tangible assets and personnel from unauthorized access, theft, vandalism, and natural disasters.

Why Physical Security Audits are Non-Negotiable
- Digital-Physical Nexus: A fortified server room can be the difference between thwarted breaches and digital disaster.
- Guarding Vital Assets: From proprietary equipment to irreplaceable documents, tangible assets are the bedrock of business operations.
- Safety Beyond Security: Beyond theft or espionage, it's about creating a secure environment where employees thrive and visitors feel safe.
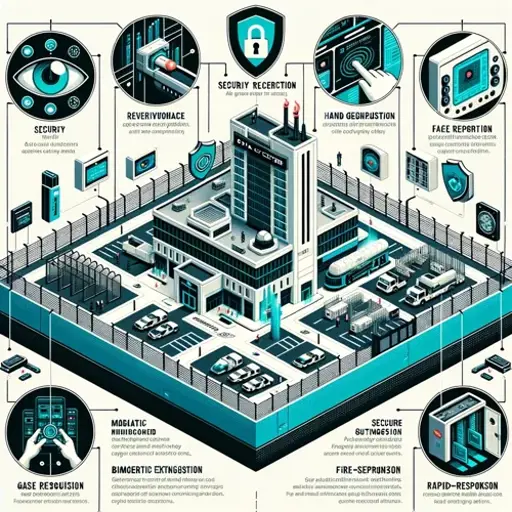
Pillars of a Physical Security Audit
- Access Mastery: Beyond barriers and locks, it's about intelligent access control systems that adapt and alert.
- Visionary Surveillance: Not just cameras, but a mesh of interconnected monitoring systems offering 360-degree vigilance.
- Guardian Personnel: Trained, vigilant, and responsive - security personnel who are the first line of defense.
- Fortified Infrastructure: A facility that stands unyielding, be it against malevolent intruders or nature's wrath.
The Intricate Dance of Physical Audits
- Evolving Adversaries: As threats mutate, so must our shields. Audits need to anticipate, not just evaluate.
- Cyber-Physical Symbiosis: Ensuring physical robustness doesn't open digital backdoors is a delicate balance.
- Efficiency Meets Fortification: Optimal security shouldn't stifle functionality but rather enhance it.
The Audit Process: From Start to Finish
The Audit Process: From Start to Finish
- Preliminary Assessment: This is the groundwork, where our team familiarizes itself with your organisation's physical layout, employee patterns, and existing security measures. It's essential to understand the foundation before building upon it.

- Risk and Vulnerability Analysis: Based on the preliminary findings, we identify potential risks and vulnerabilities. This involves both understanding the specific threats pertinent to your industry and your location's general risks, from both human adversaries and environmental factors.
- Deep Dive Inspection: Our team systematically examines every facet of your physical security infrastructure. This includes access controls, surveillance systems, alarms, barriers, lighting, and the effectiveness of security personnel. It's not just about checking for the existence of these measures but evaluating their efficiency and adaptability.
- Employee Awareness and Training Evaluation: The most advanced security measures can be rendered ineffective if personnel aren't adequately trained. We assess the awareness levels of your staff and their familiarity with security protocols, especially in emergency scenarios.

- Feedback and Recommendations: Post-inspection, we consolidate our findings into a comprehensive report. This isn't just a list of vulnerabilities but a roadmap to enhancement. Each recommendation is accompanied by actionable steps, aligned with best practices and tailored to your organization's unique requirements.
- Follow-up and Reassessment: Physical security isn't static. Once the recommended improvements are implemented, we believe in revisiting and reassessing, ensuring that the changes have fortified your defenses and that the organization is prepared for new emerging threats.
Tailoring the Audit to Your Needs
Every organization is unique, both in terms of assets and threat vectors. That's why we believe in bespoke audit solutions. Whether you're a sprawling corporate campus or a compact startup, our approach is tailored, ensuring relevance, depth, and actionable insights.

Conclusion
Physical security is as vital as its digital counterpart, acting as the first line of defense against numerous threats. As you consider fortifying your digital realms, remember the tangible domain requires equal diligence. With a comprehensive Physical Security Audit, you not only unveil vulnerabilities but pave the way for a safer, more secure operational environment.
For More Information Please Contact Us

ACCREDITATIONS






