Retail and E-commerce Sector
Quick Introduction:
In the digital age, the retail and e-commerce sector faces an ever-evolving array of cyber-security threats. With the majority of transactions now occurring online, businesses must protect not only their operational infrastructure but also, and most critically, their customers' sensitive data. The challenges range from sophisticated cyber-attacks and data breaches to internal vulnerabilities that could expose personal and financial information. With frequent high-profile data breaches, retail companies must prioritize protecting customer data to maintain trust and reputation..Staying ahead of these threats is not just a technical necessity; it’s also a legal imperative, governed by a stringent regulatory framework designed to ensure privacy, data integrity, and consumer trust.

The sector's specific cyber-security challenges include:
- Data Protection: With large volumes of personal customer data, retailers are prime targets for breaches.
- Payment Security: The need to safeguard payment information requires robust encryption and access controls.
- Supply Chain Threats: Increasing inter-connectivity with suppliers and partners expands the threat landscape.
- Phishing and Social Engineering: Employees and customers are regularly targeted through deceptive practices.
- Compliance with Regulations: The necessity to comply with multiple cyber-security standards and laws.
Cyber-security Regulations
UK-GDPR: Prioritizing Data Privacy In Retail and E-commerce
The United Kingdom General Data Protection Regulation (UK-GDPR) is the cornerstone of data protection in the UK, establishing stringent requirements for handling personal data. Retailers must ensure customer data is processed lawfully, transparently, and for specific purposes. In the event of a data breach, they are obligated to report it within 72 hours, and face significant fines for non-compliance.

Compliance Steps:
- Understand the data protection principles set out by the UK-GDPR.
- Implement adequate measures to secure personal data, such as encryption and access control.
- Ensure that there are procedures in place to handle data subject rights requests.
- Maintain detailed records of data processing activities.
- Appoint a dedicated Data Protection Officer (DPO) to oversee compliance.
- Conduct Data Protection Impact Assessments (DPIAs) for high-risk processing.
- Foster a culture of data protection awareness across the organization.
PCI-DSS: Securing Cardholder Data
The Payment Card Industry Data Security Standard is crucial for any retail business that handles credit or debit card transactions. PCI-DSS aims to secure card transactions against data theft and fraud. It specifies a set of security standards including maintaining a secure network, protecting cardholder data, implementing strong access control measures, regularly monitoring and testing networks, and maintaining an information security policy. For e-commerce retailers, demonstrating PCI-DSS compliance is not just about avoiding fines; it's about ensuring customers feel safe when providing their payment information online.

Data Protection Act 2018
While the Data Protection Act 2018 enacts the EU's GDPR into UK law, it also includes provisions that work alongside the UK-GDPR. Retailers must be aware of both sets of regulations to fully comply with the UK’s data protection regime. This Act emphasizes transparency, security, and accountability in data processing, adding layers of complexity to the already detailed UK-GDPR. Retailers need to ensure that all their data practices are transparent and secure and that they are held accountable for the data they manage.

Cyber Essentials:
The Cyber Essentials scheme is a government-backed, industry-supported initiative to help organizations protect themselves against common online threats. Achieving Cyber Essentials certification can also help retailers to address some of the compliance requirements of other standards, such as GDPR and PCI-DSS. It's particularly relevant to retailers as it addresses fundamental technical controls across five key controls:
Boundary firewalls and internet gateways
Secure configuration
Access control
Malware protection
Patch management
Certification under this scheme not only helps in safeguarding against common cyber threats but also demonstrates to customers that the retailer takes cyber-security seriously, enhancing trust and reputation.

ProCheckUp Solution's
For UK-GDPR Compliance:
- IASME Cyber Essentials: A certification that verifies basic cyber-security hygiene, ensuring that Retail and E-commerce organisations have fundamental security controls in place to protect against common cyber threats. (Learn More)
- IASME Cyber Assurance: This includes a GDPR readiness assessment to ensure that all aspects of data privacy and security are addressed, thus aligning with the GDPR’s stringent requirements.(Learn More)

For Data Protection Act 2018 Adherence:
- Data Protection Impact Assessments (DPIA): Services to help retail and e-commerce organisations conduct assessments that evaluate the impact of new projects or technologies on the privacy and security of personal data.(Learn More)
- Data Governance Consulting: Expert consultancy to ensure the correct handling of personal data across all operations, aligning with the Data Protection Act’s provisions.

For PCI-DSS Compliance:
- PCI-ASV (Approved Scanning Vendor) Services: ProCheckup, a globally recognized ASV, conducts meticulous external vulnerability scans to ensure the integrity of systems handling credit card data, in compliance with PCI-DSS requirement 11.3.2. Our ASV scan solution leverages cutting-edge security tools to rigorously test and confirm your network's defenses against known threats, helping to secure your data transactions. (Learn More)
- PCI-QSA (Qualified Security Assessor) Services: As an independent QSA firm accredited by the PCI Security Standards Council, ProCheckup embodies excellence in ensuring entities meet the stringent standards of PCI DSS. Our longstanding expertise, since the establishment of the QSA program, provides reliable validation of your compliance posture. (Learn More)
- Penetration Testing: ProCheckup's penetration testing services are an embodiment of our commitment to security excellence, meeting PCI-DSS requirement 11.4.1. Our team of Crest, Cyberscheme, and NCSC-qualified penetration testers, with a proven 24-year track record since 1999, employs a comprehensive approach to identify and remediate exploitable security vulnerabilities. (Learn More)
- Data Discovery for Primary Account Number (PAN): Our specialized services extend to the detection of PAN within your network, particularly identifying unauthorized storage locations outside the Cardholder Data Environment (CDE), adhering to PCI-DSS requirement 12.5.2. ProCheckup ensures that sensitive payment data is contained and managed securely. (Learn More)
- Segmentation Testing: With precise technical testing, ProCheckUp validates the efficacy of network segmentation, ensuring that the CDE is isolated from all systems not pertinent to card processing , in compliance with PCI-DSS requirement 11.4.5 This critical service supports PCI-DSS compliance by verifying the robustness of segmentation controls, maintaining the security of your cardholder data environment. (Learn More)
- Wireless Testing: Adhering to the stringent standards of PCI-DSS requirement 11.2.1, our team conducts comprehensive wireless testing quarterly. This process is meticulously designed to uncover and assess both sanctioned and unsanctioned wireless access points within your network, ensuring a robust security posture. (Learn More)

For Mitigating Supply Chain Vulnerabilities:
- In the current digital landscape, the inter-connectivity with suppliers and partners significantly widens the scope of potential threats. Our comprehensive Supply Chain Testing service is designed to empower businesses to identify, comprehend, and mitigate the myriad risks that stem from third-party collaborations. (Learn More)
For Combating Phishing and Social Engineering:
- The human element often presents the most significant security risk. Phishing and social engineering attacks are deceptively designed to exploit this vulnerability by manipulating individuals into divulging sensitive information or providing unauthorized access. Our proactive approach begins with in-depth Open Source Intelligence (OSINT) gathering to construct a credible pretext. We then conduct simulated phishing expeditions using realistic scenarios that mirror actual threats, thereby training your workforce to recognize and counteract such deceptive tactics effectively.(Learn More)
For Securing the Internet of Things (IoT):
- The retail sector's growing reliance on IoT devices for inventory management and enhanced customer experiences brings with it an urgent need for robust security measures. Our IoT Security Reviews are at the cutting edge, aligning with the rapid pace of digital transformation.(Learn More)
Maintaining compliance with these regulations is crucial for the retail and e-commerce sector, not just for legal integrity but also for maintaining customer trust. The assurance that a retailer is following stringent cyber-security practices can be a significant competitive advantage. Compliance ensures operational resilience, reduces the risk of financial penalties, and enhances customer confidence in the digital shopping experience.
For businesses in the retail and e-commerce sector, this means implementing robust cyber-security policies, continuously educating staff about security best practices, and regularly reviewing and updating security measures to address new and emerging threats.
Maintaining Compliance
Practical Implementation Strategies for Cyber-security in Retail:
After understanding the regulatory landscape, retail and e-commerce businesses must translate these requirements into actionable strategies. Here are key steps for retailers to take in implementing robust cyber-security measures:
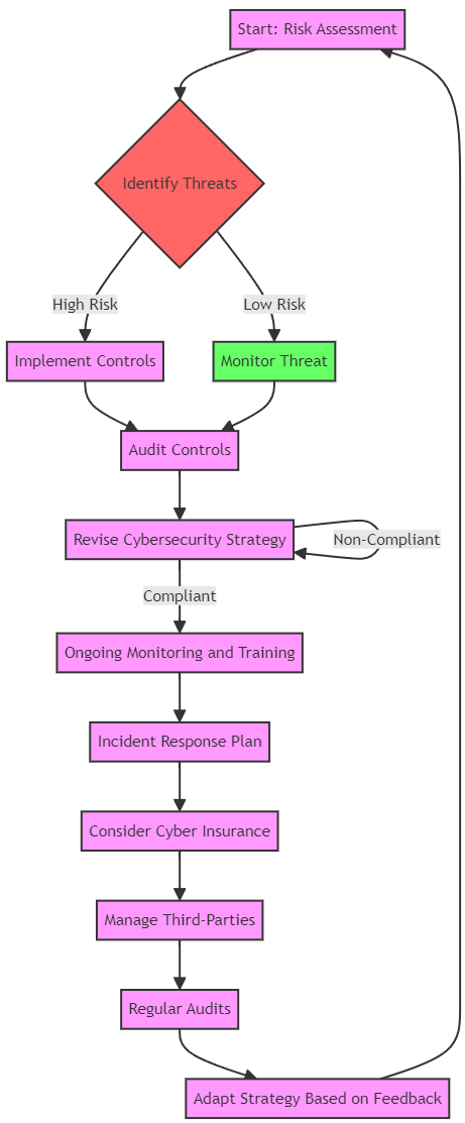
Risk Assessment and Management:
- Conduct regular and comprehensive risk assessments to identify potential vulnerabilities in the retail ecosystem, from point-of-sale systems to e-commerce platforms.
- Develop and implement a risk management strategy that includes incident response plans, regular security audits, and employee training programs
Data Encryption and Protection:
- Employ strong encryption protocols for all customer data, both in transit and at rest.
Implement additional layers of security such as tokenization and anonymization especially when handling sensitive payment information.
Access Control and Authentication:
- Ensure strict access controls are in place, allowing only authorized personnel to access sensitive data.
- Utilize multi-factor authentication to add an extra layer of security for accessing critical systems.
Employee Training and Awareness:
- Regularly train employees on the importance of cyber-security, the latest cyber threats, and safe practices for handling customer information.
- Create a culture of security where employees are encouraged to report suspicious activities without fear.
Compliance Monitoring and Review:
- Implement processes to continuously monitor compliance with cyber-security regulations.
- Schedule periodic reviews and updates of security policies to adapt to new threats and changes in the regulatory environment.
Vendor and Third-Party Management:
- Establish strict security criteria for vendors and third-party service providers.
- Regularly assess third-party risks and ensure external partners adhere to the same security standards required of the retail business itself.
Customer Data Rights and Transparency:
- Clearly communicate to customers how their data is being used, stored, and protected.
- Develop simple and efficient procedures for customers to exercise their rights under the UK-GDPR, such as accessing their data or requesting deletion.
Technology Investment and Use of Secure Platforms:
- Invest in reputable cyber-security technologies and services that offer robust defenses against cyber threats.
- Use secure e-commerce platforms that comply with industry standards and best practices for cyber-security.
By implementing these steps, retailers not only comply with regulatory requirements but also significantly strengthen their defense against cyber attacks. This commitment to cyber-security can become a competitive advantage, showcasing to customers that the retailer is trustworthy and their data is in safe hands.

Cybersecurity Process Flow Chart
Cybersecurity Collaboration and Sharing
In addition to the internal measures, it is crucial for Retail and E-Commerce organisations to actively participate in sector-wide cyber-security initiatives. These include:
- Information Sharing: Engaging in information sharing platforms to receive timely alerts on threats and share best practices with industry peers.
- Regulatory Engagement: Maintaining an open dialogue with regulators to stay ahead of new regulations and to influence policy development with real-world insights.
- Global Cybersecurity Standards: Aligning with global cyber-security standards and frameworks, such as ISO/IEC 27001, to ensure a consistent approach to managing information security.
- Cybersecurity Advocacy: Advocating for stronger cyber-security measures and more substantial investments in cyber-security at industry conferences and in public forums.

With these resources and strategies in place, retail and e-commerce providers can better anticipate and counteract the evolving cyber threats they face, ensuring trust and continuity in the digital age.
For More Information Please Contact Us

ACCREDITATIONS






