Cyber Maturity Assessment
In the rapidly evolving landscape of digital threats, understanding where your organization stands in terms of cyber-security maturity is not just an advantage—it's a necessity. Our Cyber Maturity Assessment (CMA) offers a comprehensive evaluation of your organization's cyber-security practices, policies, and procedures, bench-marked against globally recognized standards.
Why Cyber Maturity Assessment?
In today's interconnected digital ecosystem, even a minor vulnerability can result in significant damages. From reputational loss to financial implications, the stakes have never been higher. A CMA isn’t just about finding vulnerabilities; it's about understanding, planning, and setting a road-map for continual cyber-security improvement.
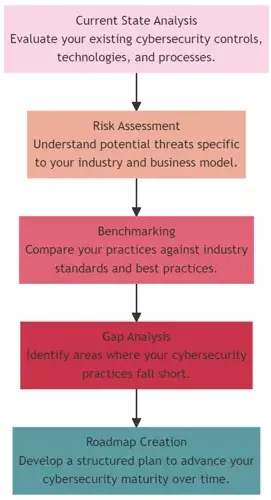
Components of Our Cyber Maturity Assessment:
- Current State Analysis: Evaluate your existing cybersecurity controls, technologies, and processes.
- Risk Assessment: Understand potential threats specific to your industry and business model.
- Benchmarking: Compare your practices against industry standards and best practices.
- Gap Analysis: Identify areas where your cybersecurity practices fall short.
- Roadmap Creation: Develop a structured plan to advance your cybersecurity maturity over time.
Benefits:
- Informed Decision Making: Understand where to invest your cybersecurity budget for maximum impact.
- Regulatory Compliance: Ensure your cybersecurity practices meet and exceed industry regulations.
- Stakeholder Confidence: Showcase your commitment to cybersecurity, earning trust from clients, partners, and stakeholders.
- Competitive Advantage: Stay ahead of competitors by ensuring that your business is protected against the latest threats.
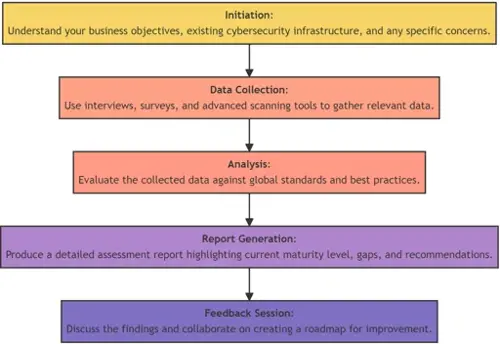
How Our CMA Process Works:
- Initiation: Understand your business objectives, existing cybersecurity infrastructure, and any specific concerns.
- Data Collection: Use interviews, surveys, and advanced scanning tools to gather relevant data.
- Analysis: Evaluate the collected data against global standards and best practices.
- Report Generation: Produce a detailed assessment report highlighting current maturity level, gaps, and recommendations.
- Feedback Session: Discuss the findings and collaborate on creating a road-map for improvement.
Who Needs a Cyber Maturity Assessment?
Whether you're a budding startup, a growing SME, or a well-established enterprise, understanding the maturity of your cybersecurity efforts is vital. This assessment is particularly beneficial for:
- Industries with strict regulatory compliance: Financial services, healthcare, energy, and others with strict data protection laws.
- Businesses undergoing digital transformation: As you integrate more digital tools and platforms, understanding security maturity becomes even more vital.
- Organizations with a high dependency on digital data: E-commerce platforms, online service providers, and other digital-first businesses.

What Sets Our CMA Apart?
- Expertise: Our team comprises professionals with years of experience and certifications in the cybersecurity domain.
- Tailored Approach: We don't believe in a 'one-size-fits-all' strategy. Our assessments are tailored to your industry and business needs.
- Actionable Insights: Beyond pointing out gaps, we offer actionable solutions to enhance your cybersecurity posture.
- Continuous Collaboration: Our relationship doesn't end with the assessment. We're here to support you in your journey towards improved cybersecurity maturity.

Frequently Asked Questions (FAQs):
Q: How long does the assessment take?
A: The duration can vary based on the size of your organization and the complexity of your digital infrastructure. Typically, it ranges from a few days to a few weeks.
Q: Will my day-to-day operations be disrupted?
A: We strive to ensure minimal disruption. Most data gathering can be done without impacting regular operations.
Q: How often should I undertake a CMA?
A: The digital threat landscape is ever-evolving. We recommend a CMA at least once a year or whenever there's a significant change in your digital operations.
For More Information Please Contact Us

ACCREDITATIONS






