Targeted Attack Resistance Assessment
Protecting your organization from sophisticated cyber threats requires a deep understanding of the tactics, techniques, and procedures employed by modern adversaries. Our Targeted Attack Resistance Assessment (TARA) evaluates your organization's ability to detect, defend, and respond to targeted attacks, ensuring that your defenses are robust enough to withstand even the most determined adversaries.
What is Targeted Attack Resistance Assessment?
TARA is an in-depth evaluation of your organization's security posture against realistic, simulated targeted cyber threats. The assessment mirrors real-world attacks, replicating the tactics and strategies employed by threat actors to identify vulnerabilities in your systems, processes, and personnel.
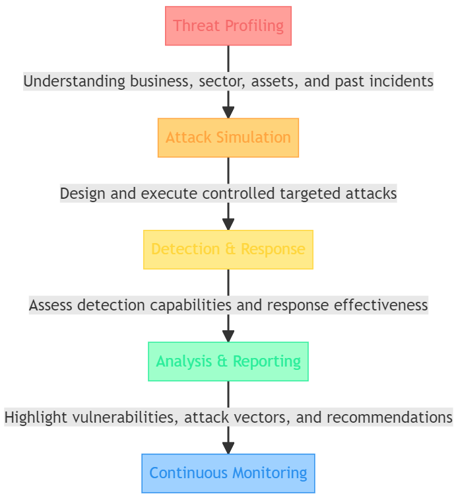
How We Approach TARA:
- Threat Profiling: We start by understanding your business and the specific threats you face. This involves understanding your sector, key assets, and any past incidents.
- Attack Simulation: Using our knowledge of the threat landscape, we design and execute a series of controlled, targeted attacks to test your defenses.
- Detection & Response: We assess your detection capabilities, the speed and effectiveness of your response, and the robustness of your remediation actions.
- Analysis & Reporting: We provide a comprehensive report highlighting vulnerabilities, successful and blocked attack vectors, and recommendations for bolstering your defenses.
- Continuous Monitoring: Post-assessment, we offer continuous monitoring solutions to ensure long-term resilience against targeted threats.
Benefits of TARA:
Proactive Defense: Understand potential weak points in your defense strategy before they're exploited.
Holistic View: Gain insights not just into technical vulnerabilities, but also process and personnel weaknesses.
Bespoke Threat Intelligence: Receive tailored threat intelligence specific to your industry and organization.
Enhanced Awareness: Boost your team's awareness and preparedness for real-world attack scenarios.
- Frequently Asked Questions (FAQs)
What differentiates TARA from a regular penetration test?
While traditional penetration tests focus on finding technical vulnerabilities, TARA goes a step further. We simulate real-world, targeted cyber threats that take into account both technical vulnerabilities and potential weaknesses in processes and personnel. The aim is to gauge how your organization would fare against a focused and determined attacker. - How often should we conduct a TARA?
For organizations at high risk of targeted attacks, such as those in critical infrastructure or holding valuable intellectual property, we recommend a semi-annual assessment. For others, an annual assessment combined with regular penetration testing and vulnerability assessments is advisable. - Will the assessment disrupt our daily operations?
Our experts work closely with your team to ensure minimal disruption. Simulations are designed to be non-destructive, and the timing can be adjusted to fit your operational requirements. - Can TARA help us with regulatory compliance?
Absolutely. A comprehensive TARA can aid in demonstrating due diligence and adherence to various regulatory standards related to cybersecurity. Furthermore, our report can be used to inform regulators of proactive security measures taken by your organization.
Take Action Now!
Don't wait for a cyber incident to reveal the vulnerabilities in your defenses. Schedule a Targeted Attack Resistance Assessment today and take a proactive step towards safeguarding your organization's future.
For More Information Please Contact Us

ACCREDITATIONS






