You’d need to be living on another planet right now to be completely unaware of what’s currently happening in Ukraine (please see here: https://www.bbc.co.uk/news/world-europe-56720589 if a reminder would be helpful). Often invasion and warfare such as this is thought of mainly in corporeal terms. For example, the initial sentence in the previously referenced article starts: ‘By air, land and sea’ but in our current world, the devastation of these attacks can often be accompanied (and preceded) by cyber warfare. It is commonly known that Ukraine has been undergoing significant cyber threats for many years and the basic timeline below aims to highlight the more recent, impacting, attacks that have been successfully launched against this European Ally.
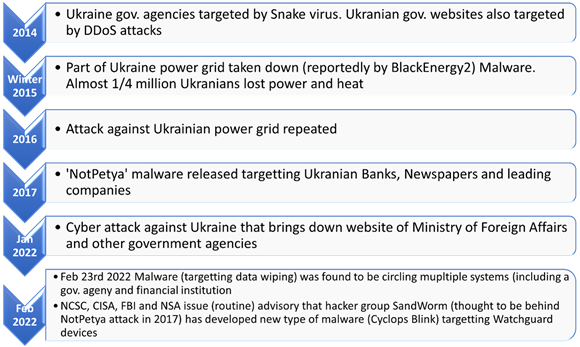
The most recent attacks (January and February 2022) draw attention with their proximity to recent current events (though it is understood there is currently no evidence for identification of the original source and investigations are underway). The attacks in January and February 2022 have been reported as including the following:
- On 14th of January 2022, multiple government websites were targeted including ministry of foreign affairs and education ministry websites where some content replaced with messages of fear for the Ukrainian people (please see https://www.theguardian.com/world/2022/jan/14/ukraine-massive-cyber-attack-government-websites-suspected-russian-hackers for further information).
- A malware attack pertaining to be ransomware was seen initially on 13 January and targeted government and technology companies – though instead of encrypting files for ransom it has been reported that file deletion was its intention. Initially identified by MSTIC (Microsoft Threat Intelligence Centre). Please see the following Microsoft URL for further information: https://www.microsoft.com/security/blog/2022/01/15/destructive-malware-targeting-ukrainian-organizations/
- On 15th of February 2022, the Ukrainian Ministry of National Defence and Armed Forces of Ukraine (as well as Privatbank and Oschadbank – state-owned banks) were targeted in a large DDoS (Distributed Denial of Service) attack (please see https://nsfocusglobal.com/reflective-and-short-burst-ddos-attacks-harnessed-to-knock-down-the-targets-in-ukraine/ for further analysis of this DDoS instance).
- February 23rd 2022 saw another DDoS (Distributed Denial of Service) attack against several government websites (including Ukrainian Ministry of Foreign Affairs, Cabinet of Ministers and Rada) as well as some Ukrainian banks (please see https://www.politico.eu/article/minister-ukraine-websites-down-in-another-massive-online-attack/ for further information). Additionally, research conducted by ESET identified that a new malware aimed at data wiping was observed within multiple Ukrainian computer systems including in the financial, defence, aviation, and IT services sectors (please see https://www.reuters.com/world/europe/ukrainian-government-foreign-ministry-parliament-websites-down-2022-02-23/, https://blog.malwarebytes.com/threat-spotlight/2022/02/cyclops-blink-malware-us-and-uk-authorities-issue-alert/ and https://www.ncsc.gov.uk/news/joint-advisory-shows-new-sandworm-malware-cyclops-blink-replaces-vpnfilter for further information).
As previously stated, cyber attack is a fully weaponized and deployed technique of modern invasion tactics and its impact against Ukraine at this current time has been clear.
What to do next? Whilst there has been a large offer of further (and ongoing) help from allies in the west (https://www.forbes.com/sites/thomasbrewster/2022/02/24/western-ukraine-cyber-aid-too-little-too-late-intelligence-expert-warns/?sh=4c97538bd5cd), it appears that Ukraine may have asked their country’s Cybercommunity for voluntary help. According to this Guardian article published 24th February 2022, Ukraine has requested help to protect critical infrastructure and conduct cyber spying missions against Russia:
https://www.theguardian.com/world/2022/feb/24/ukraine-hackers-defend-against-russia
Whilst cyberwarfare seems inevitably without an end, research and communication with, and between our ever-growing cybercommunities hopefully highlights a path to further help and hope for the future. Our thoughts go out to all of our Ukrainian friends at this awful time.



Categories